Articles
Practical guides and technical deep-dives for security professionals and system engineers.
Vector Database Performance: Benchmarking pgvector, Qdrant, and Milvus for Production RAG
Retrieval-Augmented Generation (RAG) systems live or die on the performance of their vector retrieval layer. As RAG moves from prototype to production, the choice of...

Deploying MCP Servers for AI Tool Integration: Protocol Design and Security Considerations
The Model Context Protocol (MCP) is an open standard that defines how AI models communicate with external tools and data sources. Rather than each AI...
Container Runtime Security: Seccomp Profiles, AppArmor, and Runtime Threat Detection
Container runtimes present a unique security challenge: they provide lightweight isolation, but that isolation is far thinner than a full virtual machine. A container shares...
Building an Observability Stack: Prometheus, Grafana, and Alertmanager for Infrastructure Monitoring
Modern infrastructure generates more telemetry than any human can parse manually. Prometheus, Grafana, and Alertmanager form the de facto open-source observability stack for infrastructure monitoring...
Designing a Multi-Tier PKI for Enterprise Certificate Management
A Public Key Infrastructure (PKI) is the foundation of trust in a networked environment. Every TLS certificate, code signing signature, and mutual authentication exchange depends...
Fine-Tuning vs RAG vs Prompt Engineering: Choosing the Right AI Customization Strategy
Three primary techniques exist for customizing large language model behavior to your specific domain and use cases: fine-tuning, retrieval-augmented generation (RAG), and prompt engineering. Each...

Building Autonomous AI Agents: Architecture Patterns for Multi-Step Task Execution
The promise of autonomous AI agents — systems that can decompose complex goals, select appropriate tools, recover from failures, and execute multi-step plans without human...
Automating Server Hardening with Puppet: From CIS Benchmarks to Continuous Compliance
Manual server hardening is inherently inconsistent. An engineer running a checklist at 11 PM before a deadline will miss steps. Configuration drift accumulates silently until...
Building a High-Availability Reverse Proxy with Apache and VRRP Failover
A reverse proxy is a single point of failure unless you engineer redundancy into the design from day one. Apache HTTP Server, when combined with...
Implementing Network Segmentation with pfSense VLANs and Inter-VLAN Routing
Network segmentation is one of the most effective controls in a defense-in-depth security architecture. By dividing a flat network into isolated broadcast domains, organizations limit...
AI-Powered Security Operations: Building Detection Rules from Threat Intelligence with LLMs
Introduction The modern threat intelligence ecosystem produces data at a scale that overwhelms human analysts. A single STIX/TAXII feed can deliver hundreds of indicators per...
Running Production LLMs on Consumer Hardware: Quantization, Context Management, and Inference Optimization
Introduction Until 2023, running a capable language model locally required enterprise GPU hardware costing tens of thousands of dollars. The quantization revolution changed that equation...
Designing a Self-Hosted SSO Platform with Authentik: OIDC, SAML, and Proxy Authentication
Introduction Single sign-on is no longer a luxury reserved for large enterprises with dedicated identity teams. The combination of SaaS-based identity providers (Okta, Auth0, Azure...
Deploying Wazuh Agents Across Heterogeneous Fleets: Linux, Windows, FreeBSD, and Containers
Introduction Wazuh is an open-source SIEM and host-based intrusion detection platform that scales from a handful of servers to tens of thousands of endpoints. Its...
Building a Multi-Site Backup Strategy with ZFS Snapshots and Encrypted Offsite Replication
Introduction Data loss is not a question of if, but when. Hardware failures, ransomware attacks, accidental deletions, and datacenter outages are realities every infrastructure team...
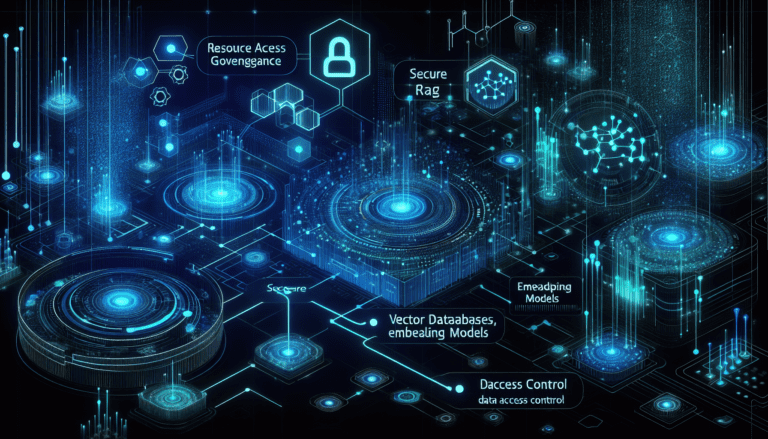
Building Secure RAG Pipelines: Vector Databases, Embedding Models, and Data Access Control
Building Secure RAG Pipelines: Vector Databases, Embedding Models, and Data Access Control Retrieval-Augmented Generation (RAG) has become the standard architecture for LLM applications that need...
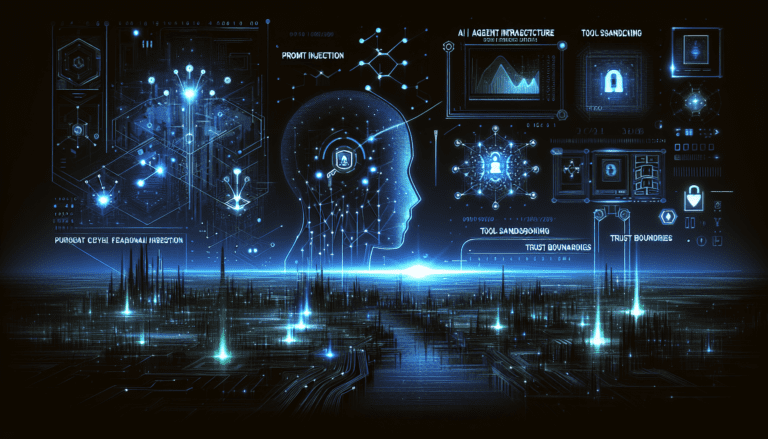
Securing AI Agent Infrastructure: Prompt Injection, Tool Sandboxing, and Trust Boundaries
Securing AI Agent Infrastructure: Prompt Injection, Tool Sandboxing, and Trust Boundaries AI agents — systems that combine large language models with tool use, memory, and...

Hardening Linux Containers: LXC/LXD Security Profiles for Production Workloads
Hardening Linux Containers: LXC/LXD Security Profiles for Production Workloads Linux containers — whether managed by LXC, LXD, or Proxmox PCT — offer significantly lower overhead...
Automated Certificate Management for Internal Infrastructure
Automated Certificate Management for Internal Infrastructure Certificate management is one of those operational burdens that accumulates silently until it doesn't. A forgotten certificate expiry takes...
Zero Trust Network Segmentation with VLANs and Firewall Policies
Zero Trust Network Segmentation with VLANs and Firewall Policies The perimeter-based security model — the idea that everything inside your network is trusted — has...
Rate Limiting and API Abuse Prevention: Patterns That Scale
A hands-on guide to scalable API abuse prevention using token buckets, sliding windows, Redis-backed distributed counters, layered identity strategies, graceful degradation, and telemetry that helps defenders distinguish noisy clients from real attacks.
Forensic Readiness: Preparing Your Infrastructure Before the Breach
A practical blueprint for building forensic readiness before an incident, including centralized logging, evidence preservation, disk and memory capture planning, timestamp discipline, and chain-of-custody procedures that hold up under pressure.
Kubernetes Network Policies: Building Microsegmentation That Actually Works
A technical guide to implementing Kubernetes network policies with default-deny baselines, namespace isolation, careful service-to-service exceptions, and validation methods that keep microsegmentation enforceable instead of theoretical.
Designing a Secure Self-Hosted Git Infrastructure: Beyond GitHub
A practical, sanitized guide to building self-hosted Git services with strong identity controls, signed commits, branch protection, secret scanning, and safer CI/CD integration for teams that need more control than a hosted forge provides.
Sysmon for Linux: Deploying Process-Level Telemetry Across Your Fleet
A sanitized, example-driven guide to rolling out Sysmon for Linux for process, network, and file telemetry, then shipping the signal into a SIEM pipeline that helps defenders spot living-off-the-land activity without drowning in noise.
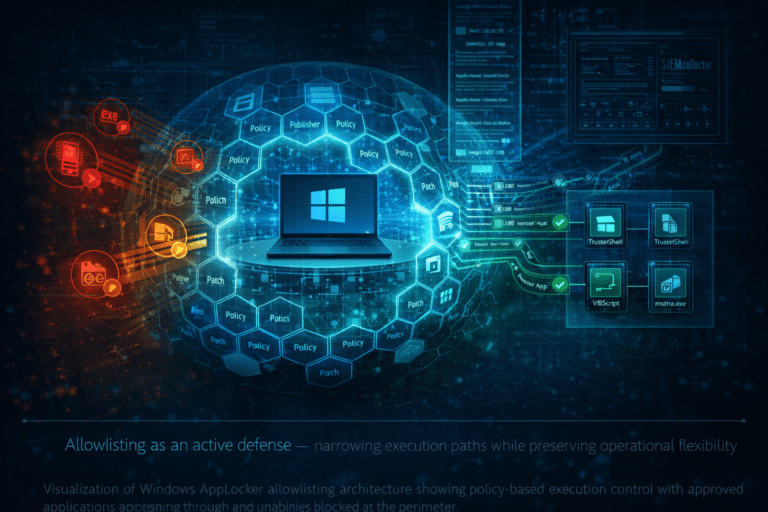
Windows Endpoint Security with AppLocker: Building a Practical Allowlisting Baseline
A sanitized, example-driven guide to rolling out AppLocker in a Windows environment, starting with inventory, audit-first policy design, event collection, controlled enforcement, and operational guardrails that keep defenders ahead of commodity malware and script abuse.
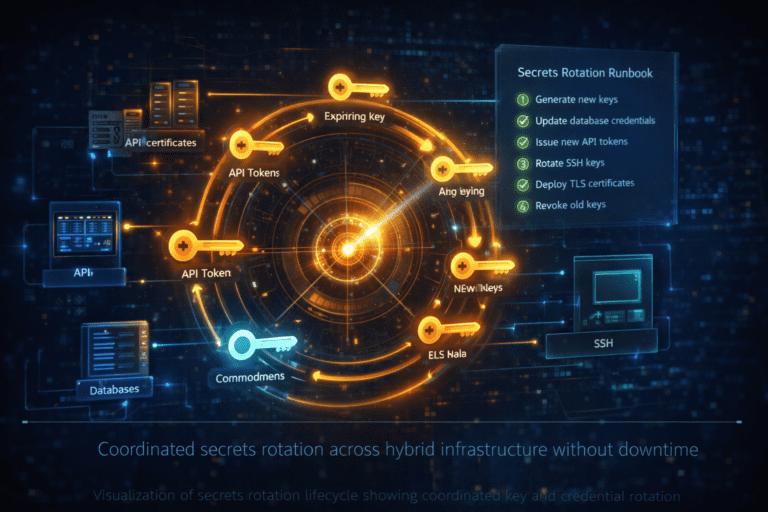
Secrets Rotation Runbooks for Hybrid Infrastructure
A practical, sanitized walkthrough for designing and executing repeatable secrets rotation runbooks across on-prem and cloud systems, with example inventories, maintenance windows, validation steps, and rollback patterns that security teams can adapt to their own environments.
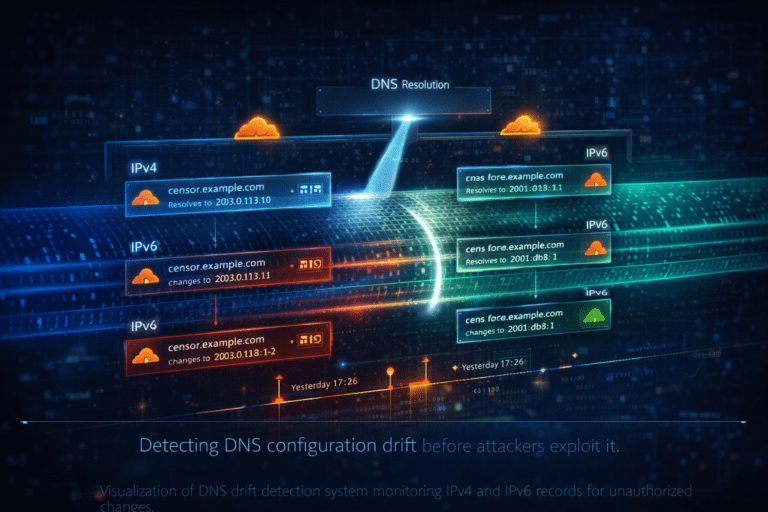
Building a DNS Drift Detection Workflow for Dual-Stack Security Monitoring
A practical, sanitized walkthrough for detecting DNS record drift, validating dual-stack exposure, and feeding high-signal findings into a SIEM using only fictional infrastructure and example data.
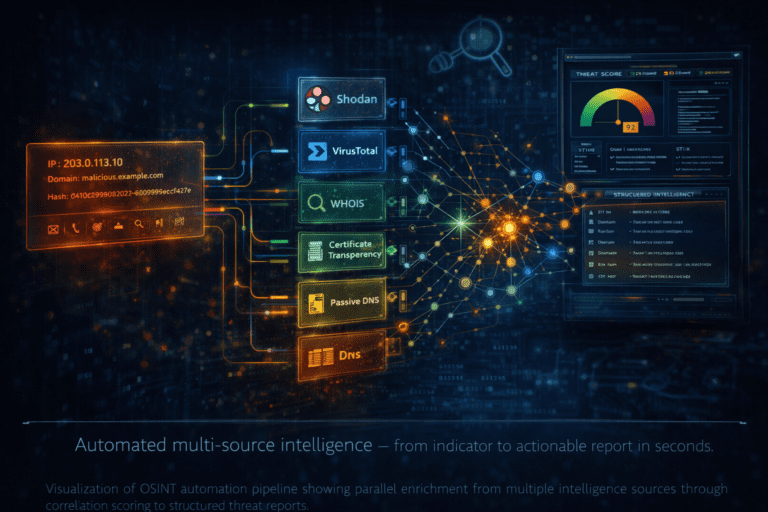
Building OSINT Automation Pipelines for Threat Research and Incident Response
Build modular OSINT pipelines with parallel enrichment, correlation scoring, STIX output, and threat intel platform integration.
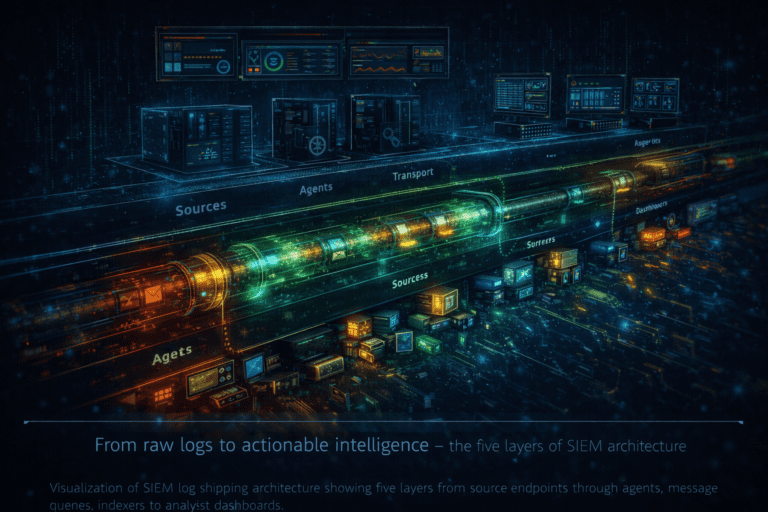
SIEM Log Shipping Architecture: From Agent to Dashboard at Scale
Design a log shipping architecture for mixed environments — agents, message queues, indexers, retention policies, and capacity planning.

Deploying Suricata IDS Behind pfSense: Network Intrusion Detection for Self-Hosted Infrastructure
Deploy Suricata as a network IDS sensor — span port setup, custom rules for lateral movement and C2 detection, SIEM integration.

Cloudflare as a Security Layer: Proxying, WAF, DDoS Protection, and DNS Management
Using Cloudflare as the security perimeter for self-hosted infrastructure — WAF rules, DDoS protection, origin lockdown, and API-driven DNS.
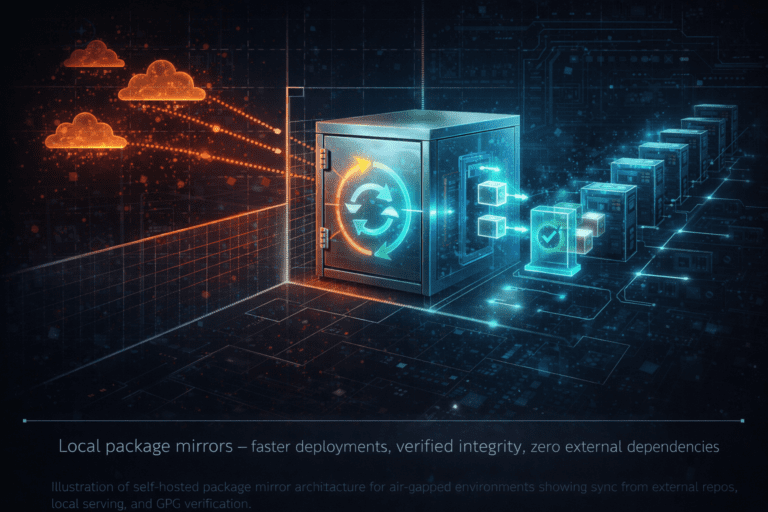
Building a Self-Hosted Package Mirror for Air-Gapped and Hardened Environments
Set up an internal apt mirror for air-gapped networks — apt-mirror, nginx serving, GPG keys, fleet automation, and troubleshooting.
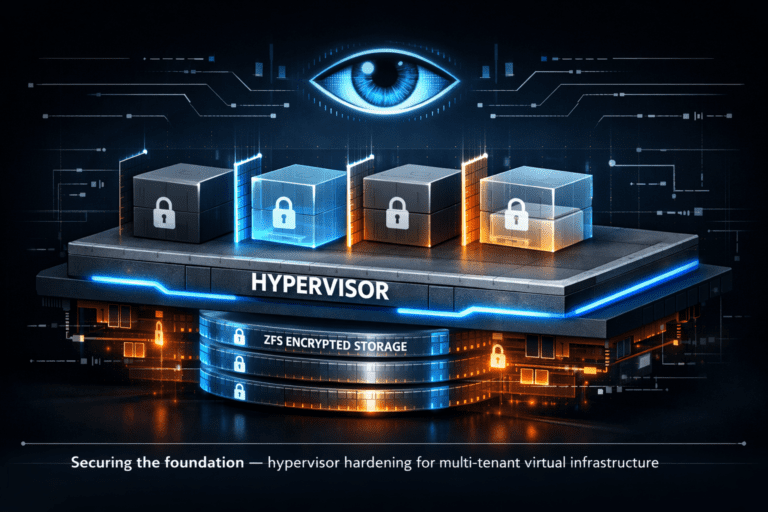
Proxmox Virtualization Security: Hardening the Hypervisor Layer for Multi-Tenant Environments
Secure Proxmox VE — ZFS encryption, network segmentation, API controls, LXC vs KVM isolation, and hypervisor integrity monitoring.
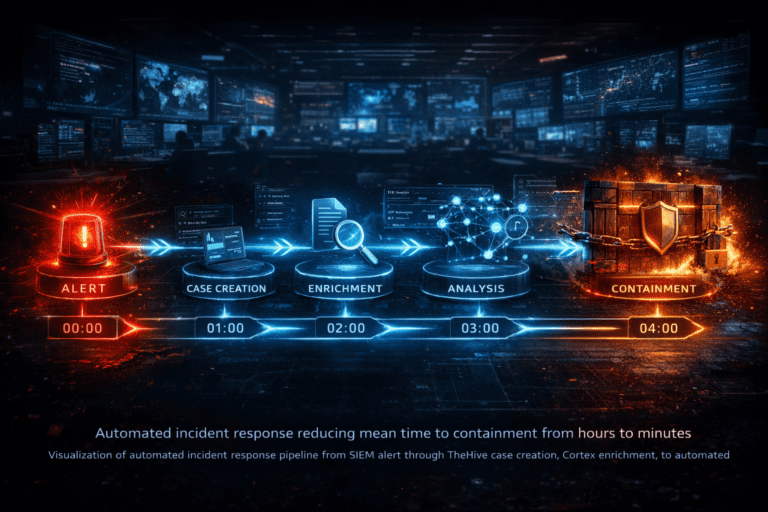
Incident Response Automation with TheHive and Cortex: From Alert to Containment in Minutes
Build an automated IR pipeline — SIEM alerts to TheHive cases, Cortex enrichment, and playbook-driven containment actions.
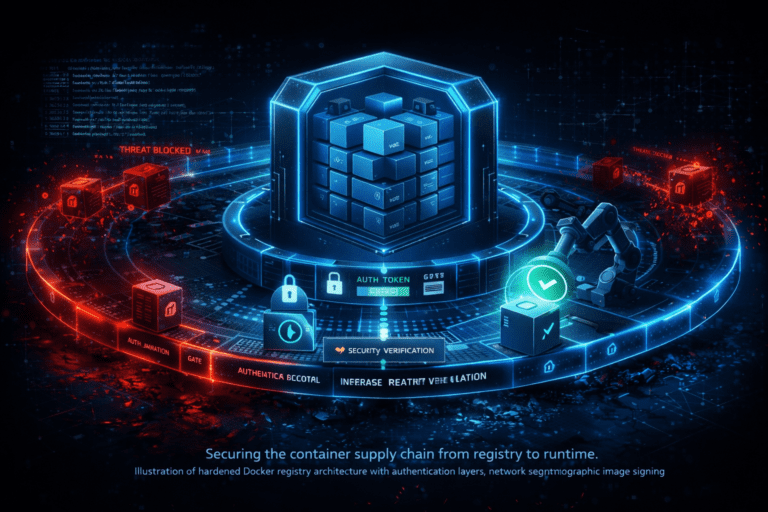
Self-Hosted Docker Registry Hardening: Authentication, Network Segmentation, and Image Signing
Harden your private Docker registry — token auth, image signing with Cosign, vulnerability scanning, and proxy buffer tuning.
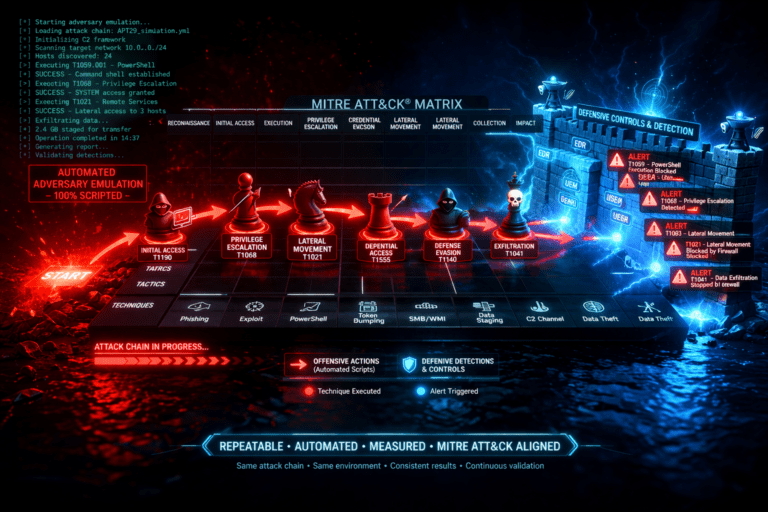
Automated Adversary Emulation: Building a Repeatable Penetration Testing Framework
Build an internal adversary emulation framework mapped to MITRE ATT&CK — automated attack chains, safety controls, and detection validation.
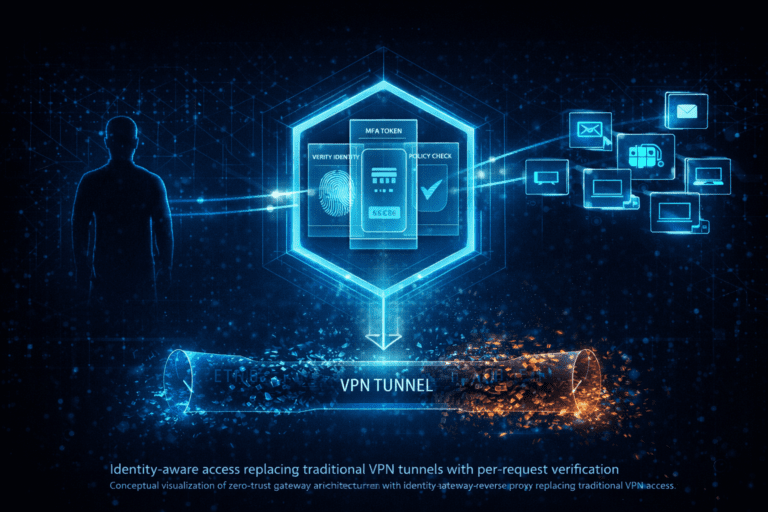
Authentik SSO as a Zero-Trust Gateway: Replacing VPNs with Identity-Aware Reverse Proxies
Implement BeyondCorp-style zero-trust access with self-hosted Authentik — OIDC, per-app policies, MFA enforcement, and VPN migration.
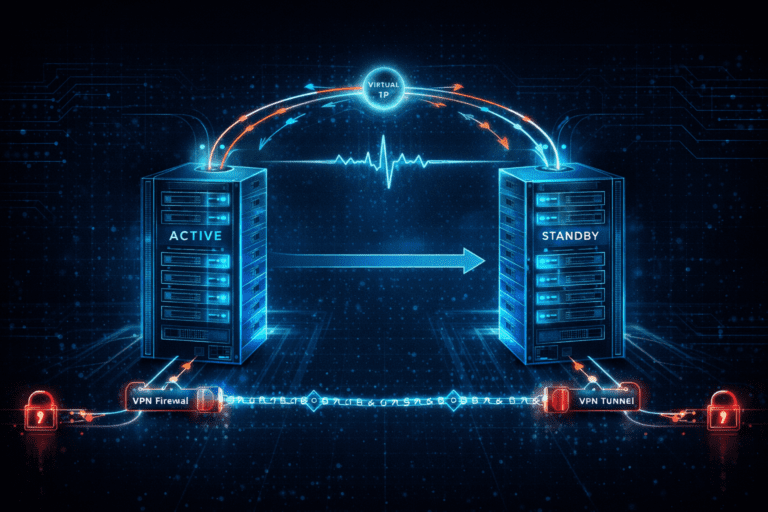
Dual Firewall HA with pfSense CARP: Design, Failover Testing, and Kill Switch Patterns
Design and operate a high-availability firewall cluster with pfSense CARP, automated failover testing, and VPN kill switches.
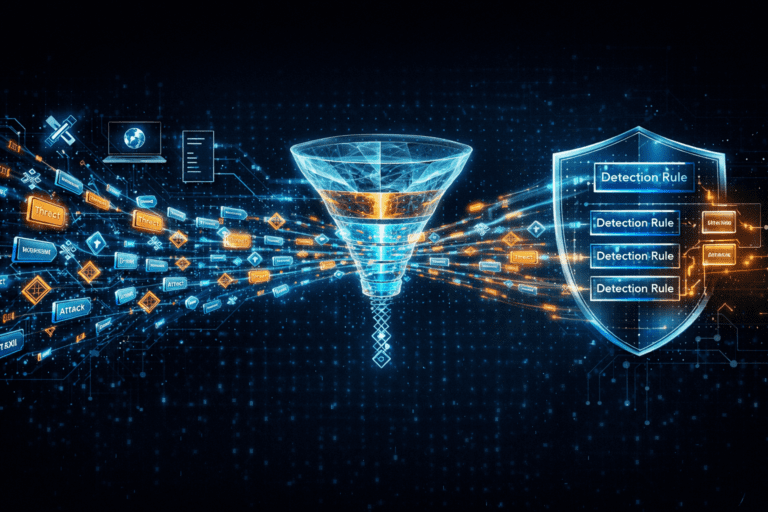
Practical Threat Intelligence Automation: From STIX/TAXII Feeds to Actionable SIEM Rules
Build an automated pipeline from threat feeds to SIEM detection rules — IOC correlation, confidence scoring, and false positive tuning.
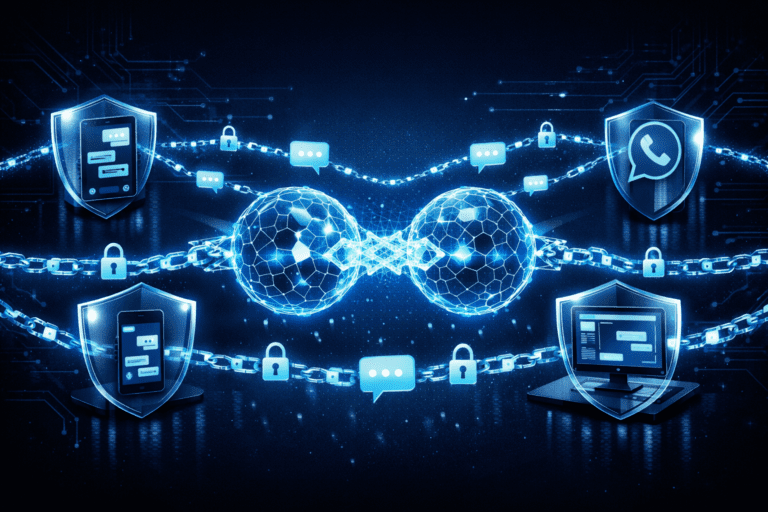
Building an Air-Gapped E2EE Communications Platform with Matrix and Signal Bridges
Deploy Matrix/Synapse with E2EE bridges to Signal, WhatsApp, and Slack — key verification, metadata exposure, and media store hardening.
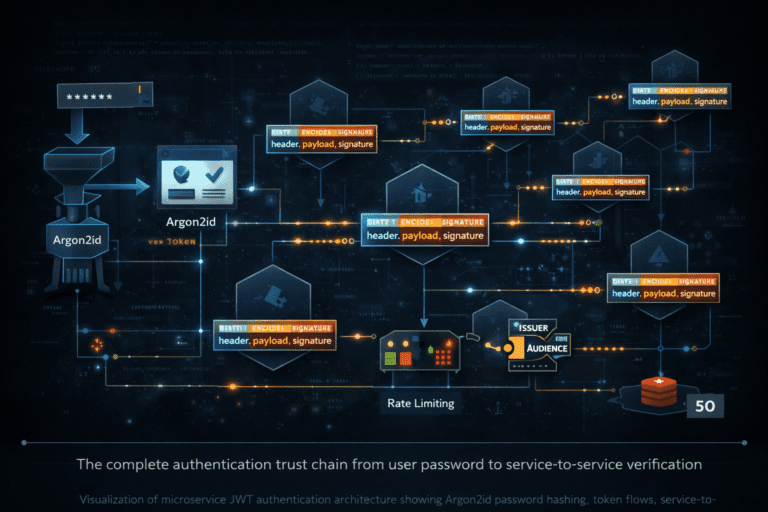
Securing Microservice Authentication: JWT Patterns, Service Tokens, and the Credential Trust Chain
Deep dive into JWT-based auth for microservices — Argon2id password hashing, service-to-service tokens, rate limiting, and common vulnerabilities.

Building a Wazuh-Powered SOC on a Budget: From Log Collection to Automated Response
End-to-end guide to deploying Wazuh as the core of a security operations center — agents, custom rules, active response, and SIEM integration.
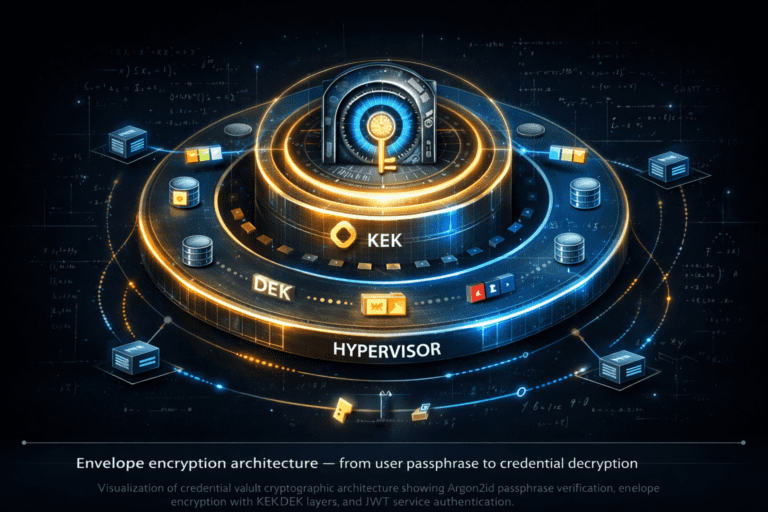
Credential Vault Architecture: Designing a Cryptographic Trust Anchor for Microservices
How to build a credential vault with envelope encryption, Argon2id passphrase verification, and JWT service authentication — the complete cryptographic chain.

Why Configuration Management Still Matters: Infrastructure Hardening with Puppet
A practical guide to using Puppet for continuous security enforcement — SSH hardening, kernel tuning, audit compliance, firewall management, and SIEM integration.

Hardening SSH Banners on Internet-Facing Bastion Hosts
Stop leaking system info through SSH banners.
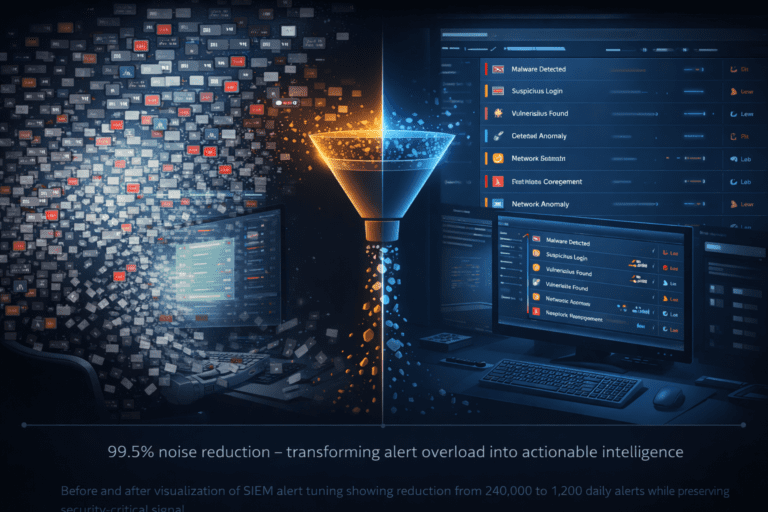
Wazuh SIEM Alert Tuning: From 240K to 1,200 Alerts Per Day
How to reduce Wazuh alert noise by 99.5% while preserving signal.
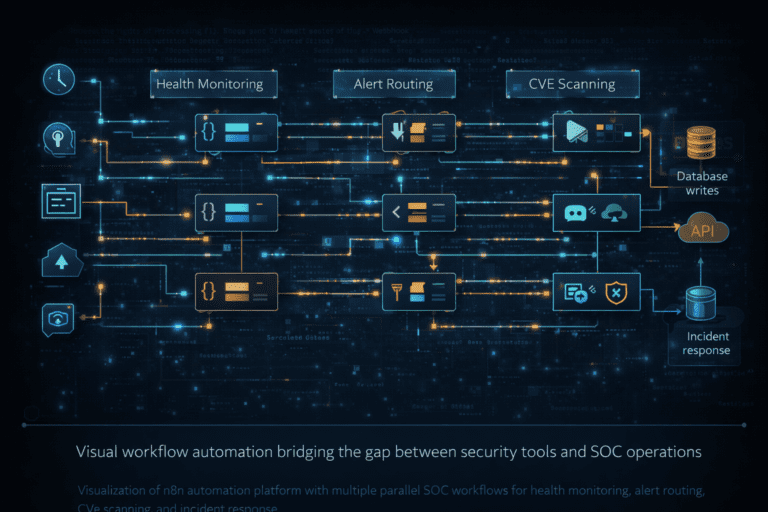
Building a Multi-Workflow n8n Automation Platform for SOC Operations
A practical guide to deploying n8n for security operations.
